Messages Exchanged During SSL Handshake
- The Master Secret Is Used To Generate Session Keys In Minecraft
- The Master Secret Is Used To Generate Session Keys In Windows 10
- The Master Secret Is Used To Generate Session Keys In Word
- The Master Secret Is Used To Generate Session Keys 2016
The following steps describes the sequence of messages exchanged duringan SSL handshake. These step describe the programmatic details of the messagesexchanged during the SSL handshake.
The client sends the server the client’s SSL versionnumber, cipher settings, randomly generated data, and other information theserver needs to communicate with the client using SSL.
The server sends the client the server’s SSL versionnumber, cipher settings, randomly generated data, and other information theclient needs to communicate with the server over SSL. The server also sendsits own certificate and, if the client is requesting a server resource thatrequires client authentication, requests the client’s certificate.
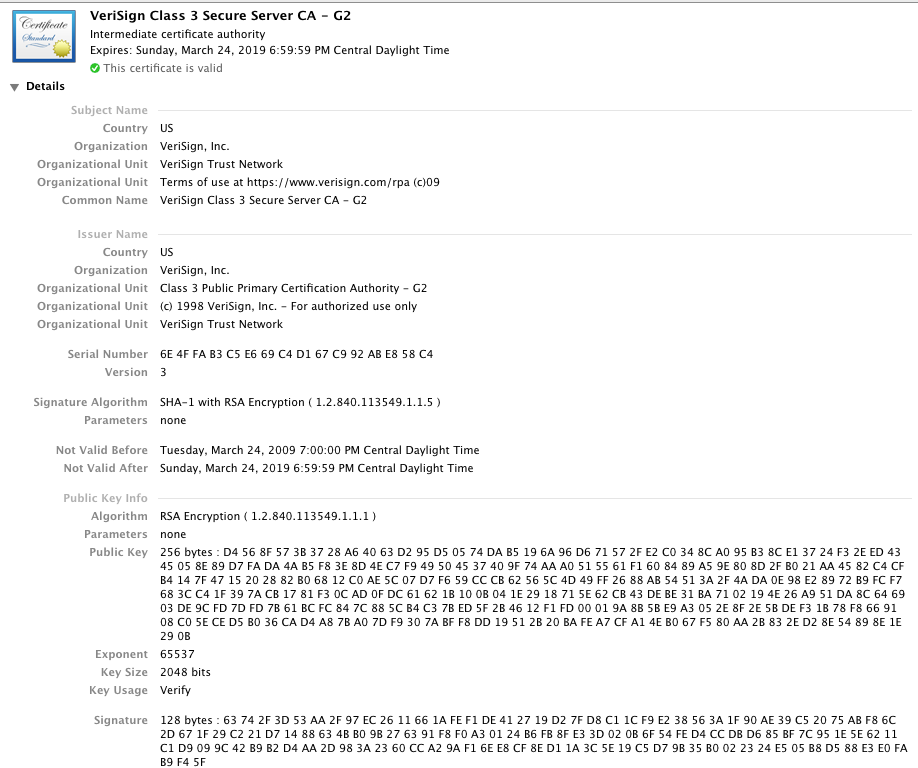
The client can use some of the information sent by the serverto authenticate the server. For details, see Server Authentication During SSL Handshake. If the server cannot be authenticated,the user is warned of the problem and informed that an encrypted and authenticatedconnection cannot be established. If the server can be successfully authenticated,the client goes on to Step 4.
Using all data generated in the handshake so far, the client,with the cooperation of the server, depending on the cipher being used, createsthe pre-master secret for the session, encrypts it with the server’spublic key, obtained from the server’s certificate, sent in Step 2,and sends the encrypted pre-master secret to the server.
If the server has requested client authentication (an optionalstep in the handshake), the client also signs another piece of data that isunique to this handshake and known by both the client and server. In thiscase the client sends both the signed data and the client’s own certificateto the server along with the encrypted pre-master secret.
If the server has requested client authentication, the serverattempts to authenticate the client. For details, see Server Authentication During SSL Handshake. If the client cannot be authenticated,the session is terminated. If the client can be successfully authenticated,the server uses its private key to decrypt the pre-master secret, then performsa series of steps (which the client also performs, starting from the samepre-master secret) to generate the master secret.
Both the client and the server use the master secret to generatethe session keys, which are symmetric keys used to encryptand decrypt information exchanged during the SSL session and to verify itsintegrity—that is, to detect changes in the data between the time itwas sent and the time it is received over the SSL connection.
The client sends a message to the server informing it thatfuture messages from the client are encrypted with the session key. It thensends a separate (encrypted) message indicating that the client portion ofthe handshake is finished.
The server sends a message to the client informing it thatfuture messages from the server are encrypted with the session key. It thensends a separate (encrypted) message indicating that the server portion ofthe handshake is finished.
The SSL handshake is now complete, and the SSL session hasbegun. The client and the server use the session keys to encrypt and decryptthe data they send to each other and to validate its integrity.
The Master Secret Is Used To Generate Session Keys In Minecraft
Before continuing with a session, directory servers can be configuredto check that the client’s certificate is present in the user’sentry in an LDAP directory. This configuration option provides one way ofensuring that the client’s certificate has not been revoked. /windows-server-2012-essentials-product-key-generator.html.
The Master Secret Is Used To Generate Session Keys In Windows 10
The SSL or TLS handshake enables the SSL or TLS client and server to establish the secret keys with which they communicate. This section provides a summary of the steps that enable the SSL or TLS client and server to communicate with each other: Agree on the version of the protocol to use. Select cryptographic algorithms. The client creates a random Pre-Master Secret and encrypts it with the public key from the server's certificate, sending the encrypted Pre-Master Secret to the server. The server receives the Pre-Master Secret. The server and client each generate the Master Secret and session keys based on the Pre-Master Secret. Managing Keys in AWS CloudHSM. Generate Keys. To generate keys on the HSM, use the command that corresponds to the type of key that you want to generate. To import a secret key. Use the genSymKey command to create a wrapping key. The following command creates a 128-bit AES wrapping key that is valid only for the current session.
Both client and server authentication involve encrypting some pieceof data with one key of a public-private key pair and decrypting it with theother key:
The Master Secret Is Used To Generate Session Keys In Word
The Master Secret Is Used To Generate Session Keys 2016
In the case of server authentication, the client encryptsthe pre-master secret with the server’s public key. Only the correspondingprivate key can correctly decrypt the secret, so the client has some assurancethat the identity associated with the public key is in fact the server withwhich the client is connected. Otherwise, the server cannot decrypt the pre-mastersecret and cannot generate the symmetric keys required for the session, andthe session is terminated.
In the case of client authentication, the client encryptssome random data with the client’s private key—that is, it createsa digital signature. The public key in the client’s certificate cancorrectly validate the digital signature only if the corresponding privatekey was used. Otherwise, the server cannot validate the digital signatureand the session is terminated.