May 28, 2015 This blog describes how to generate a private/public key pair using GPG version 1.4.5. The resulting public key will contain two keys, one key for signing and a subkey for encryption. This key can be used with HCM Fusion SaaS to encrypt/decrypt files as they are transferred to. The PGP keys generated by Enigmail automatically expire after five years. So if you lose all your files, you can hope that people will know to ask you for another key once the key has expired. You might have a good reason to disable the PGP key before it expires. Perhaps you want to generate a.
Part 0 – Introduction
Here’s my basic guide for PGP on OS X. The OS in question is OS X 10.9 Mavericks, but it should still work for other versions. As for the tool itself, we’ll be using GPG Suite Beta 5. This is my first time using OS X in… years. If you see anything I’m doing wrong, or could be done easier, feel free to correct me in the comments.

If you’ve done your research, you’ll see it’s not recommended to do anything darknet related on OS X, but I’m not going to go over the details here. You’ve obviously made your decision.
Part 1 – Installing the software
Like I said above, we’ll be using GPG Suite Beta 5. If you’re curious and want to see the source code, you can do so here.
- Head on over to https://gpgtools.org, and download ‘GPG Suite Beta 5′
- Open the file you downloaded, you should see this screen. Double click on ‘Install’
- Follow the installation process. If successful, you should see this screen. You can now close the window
Part 2 – Creating your keypair
GPG Suite actually makes this a super simple process. Just like the Linux guide, we’ll be using 4096 bit length for encryption.
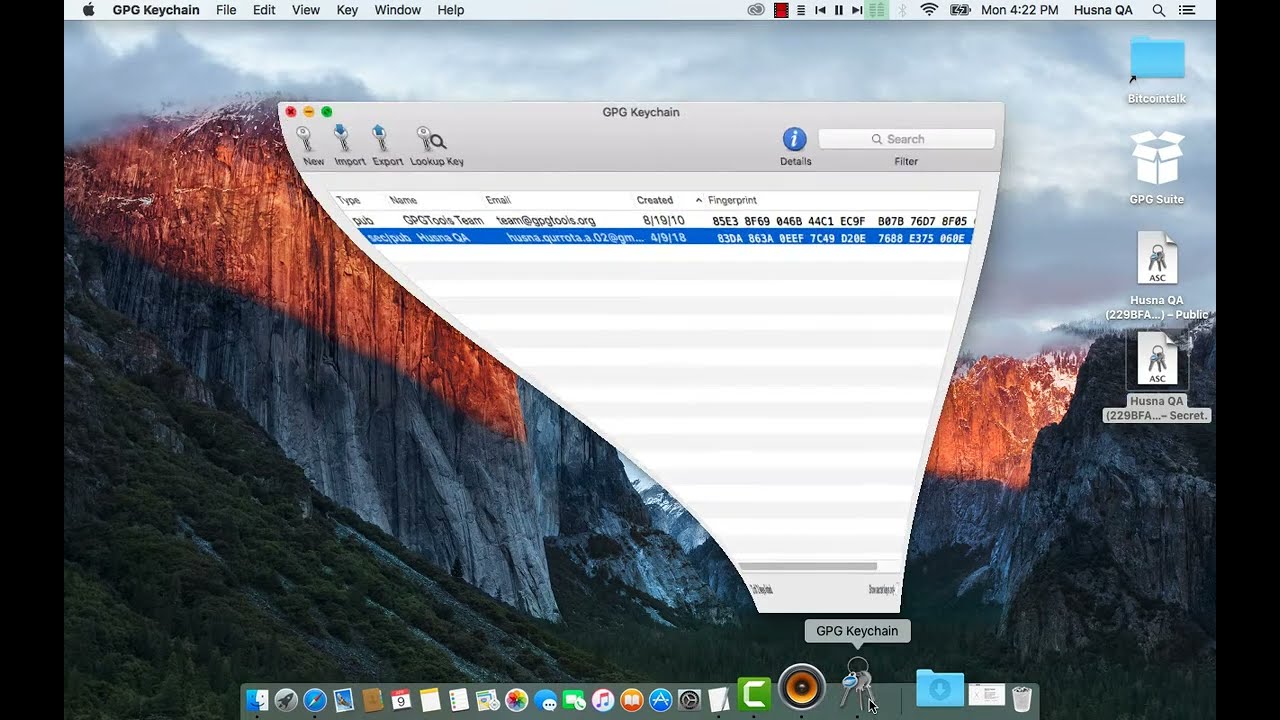
- Open up GPG Keychain, you should be greeted by this beautiful window
- Click ‘New’ at the top left of the window
- You should see a small popup. Click the arrow beside ‘Advanced options’, make sure the key length is 4096. For our purposes, we’ll uncheck ‘key expires’. Put your username where it says ‘full name’, fill out what you want for email, and create a secure passphrase. Check the picture for an example on how to fill it out. When complete, click ‘Generate key’
- GPG Keychain will begin generating your key. Move the mouse around, mash keys in a text editor, have something downloading. Do random stuff to create entropy for a secure key.
- annndddddd we’re done!
Part 3 – Setting up the environment
This is where OS X differs from other platforms. The suite itself doesn’t provide a window to encrypt/decrypt messages, so we need to enable some options.
- Go into system preferences, open up ‘Keyboard’
- You should see this window. Click the ‘Keyboard Shortcuts’ tab at the top, then ‘Services’ in the left pane. Scroll down in the right pane to the subsection labeled ‘Text’, and to the OpenPGP options. Here you can create keyboard shortcuts. We’ll uncheck everything OpenPGP that’s under ‘Text’, and delete their shortcuts. Now we’ll enable ‘Decrypt’, ‘Encrypt’, and ‘Import key’. Create keyboard shortcuts for these if you wish. Check the picture to make sure you’re doing everything correctly. You can now close the window.
Part 4 – Obtaining your public key
This part is super simple.
- Open up GPG Keychain, select your key
- At the top of the window, click ‘Export’
- Give it a name, make sure ‘include secret key in exported file’ is unchecked, and click ‘save’
- Open your text editor of choice, browse to where you saved the key, open it
- There it is. Copy and paste this on your market profile to make it easier for people to contact you
Part 5 – Obtaining your private key
Again, super simple.
- Open up GPG Keychain, select your key
- At the top of the window, click ‘Export’
- Keep the file name it gives you, check ‘Include secret key in exported file’, then click save
Keep this file in a safe place, and don’t forget your passphrase. You’re fucked without it!
Part 6 – Importing a public key
This is really easy.
- Find the key you want to import.
- Copy everything from ‘—–BEGIN PGP PUBLIC KEY BLOCK—–‘ to ‘—–END PGP PUBLIC KEY BLOCK—–‘
- Paste it into your favourite text editor, highlight everything, right click, go to ‘Services’, then ‘OpenPGP: Import key’
- You’ll see this window pop up confirming the key has been imported, click ‘Ok’
- Open up GPG Keychain just to confirm the key is there
Part 7 – Importing a private key
Again, really easy.
- Open GPG Keychain, click ‘Import’ at the top
- Browse to where your key is, click it, then click ‘Open’. It should have a .asc file extension
- You’ll see this pop up confirming your key has been imported. Click ‘Close’
Part 8 – Encrypting a message
- Open your text editor of choice, write your message
- Highlight the message, right click, ‘Services’, ‘OpenPGP: Encrypt’
- A window should appear. Select who you’re sending it to, sign it with your key if you wish, click ‘Ok’
- Copy everything, and send it to the recipient
Part 9 – Decrypting a message
Pretty much the same process as encrypting
- Open your text editor of choice, paste the message
- Highlight everything, right click, ‘Services’, ‘OpenPGP: Decrypt’
- A window should pop up. Enter your passphrase, then click ‘Ok’
- aannnddddd there’s your message
Part 10 – Conclusion
That wasn’t too hard, was it? Like I said in the intro, you shouldn’t be using OS X for DNM activities due to privacy issues, but I won’t go into it. This took forever to complete because OS X is a bitch to get running properly in a virtual machine. A guide for Windows will be coming next week!
Shortlink: drk.li/472
GNU gpg is encryption and signing tool.
The GNU Privacy Guard (GnuPG or GPG) is a free software replacement for the PGP suite of cryptographic software.
GnuPG encrypts messages using asymmetric keypairs individually generated by GnuPG users. The resulting public keys can be exchanged with other users in a variety of ways, such as Internet key servers. They must always be exchanged carefully to prevent identity spoofing by corrupting public key ↔ ‘owner’ identity correspondences. It is also possible to add a cryptographic digital signature to a message, so the message integrity and sender can be verified, if a particular correspondence relied upon has not been corrupted.
How do I create my own GnuPG private and public key
1) Login to your shell account
2) Use gpg command to create the keys$ gpg --gen-key
Output:
3) Now keys generated, you can list your own key using:$ gpg -K
OR$ gpg --list-keys
Output:
Let us try to understand the line pub 1024D/CA7A8402 2007-02-10:
- pub : Public key
- 1024D : The number of bits in the key
- CA7A8402 : The key ID
- 2007-02-10 : The date of key creation
- Vivek Gite : The user real name
- <vivek@nixcraftcorp.com> : The email id
Most important is the key ID i.e. CA7A8402. Make sure you use powerful passphrase to protect keys and not the easy one.
4) To list secret key, type the command:$ gpg --list-secret-keys
Output:
Mac Os X Generate Pgp Keys Windows 10
ADVERTISEMENTS